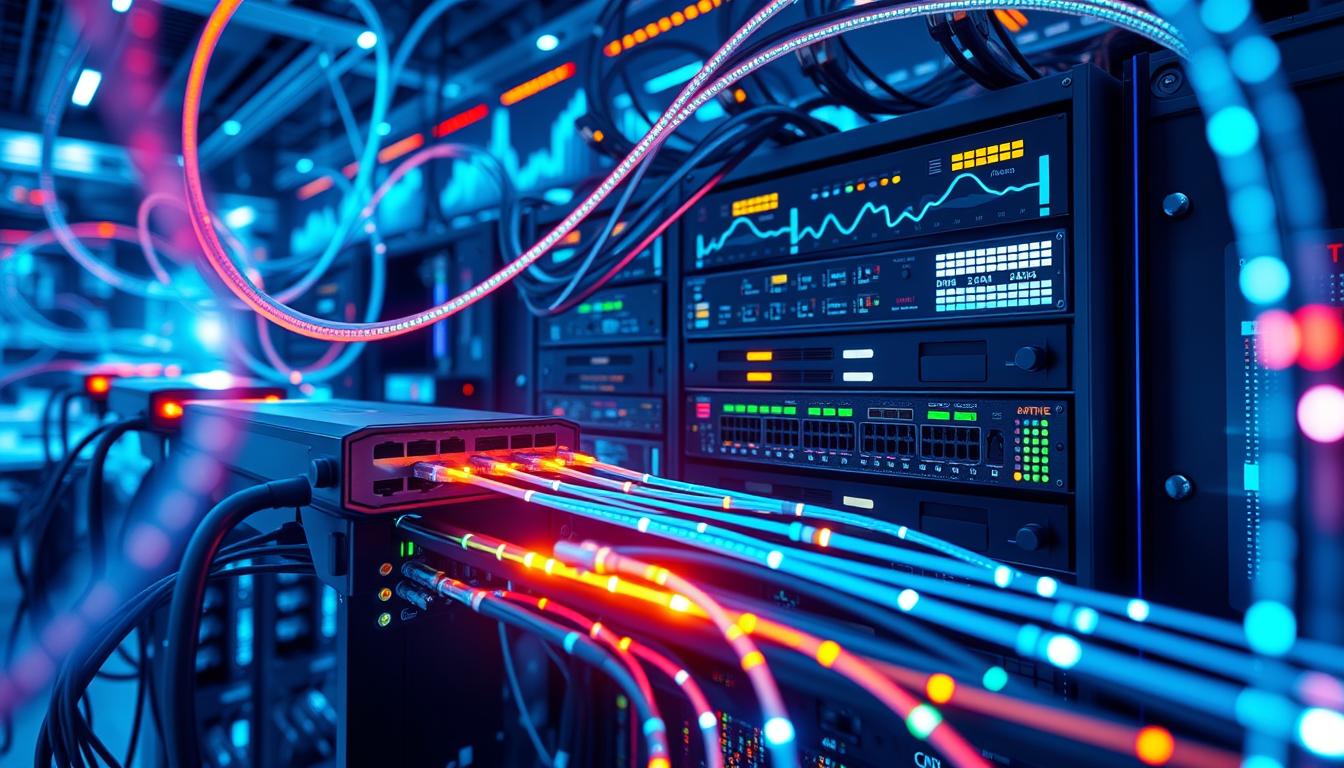
Trunking is a crucial concept in modern telecommunications, particularly for businesses that require high-speed, reliable data transfer within their network. A trunk is a communication channel that can carry multiple signals at once, allowing for efficient communication between devices. In this article, we will explore the basics of trunking, including its importance in communication, types of trunks, and how to maximize their efficiency. Additionally, we will discuss best practices for configuring and securing trunks, as well as how to migrate to cloud-based trunking smoothly.
Understanding Trunking in Telecommunications
Trunking is a method of combining multiple communication channels into a single connection for transmission between devices. By leveraging trunks, companies can save time, reduce expense, and increase efficiency across their network.
The Basics of Trunking and Its Importance in Communication
Trunking is a crucial component of modern telecommunications, especially in business environments where high-speed data transfer is an essential requirement. Trunks are used to combine multiple communication channels into a single connection that can transmit and receive data between devices at a much faster rate than traditional connections. These channels can come in many different forms, including voice, video, and data. The primary benefit of trunks is that they reduce the number of connections required within a network, resulting in a more efficient flow of data and a reduction in hardware expenses. Additionally, trunks can be used to improve security by creating a single point of entry for network traffic, making it easier to monitor and control data flow.
Trunking is also used in the telecommunications industry to provide a more reliable and scalable network infrastructure. With the increasing demand for high-speed data transfer and the rise of cloud computing, companies need to ensure that their network can handle the traffic and provide a seamless experience for their users. Trunks can be configured to provide redundancy and failover capabilities, ensuring that the network remains operational even in the event of a failure. This is particularly important for businesses that rely on their network for critical operations, such as financial institutions or healthcare providers.
Configuring Trunks for Optimal Performance
While trunks are essential for efficient communication in modern telecommunications, it is essential to configure them correctly to optimize their performance. There are different types of trunking protocols with varying levels of performance and features. The most common protocols used in trunking are the VLAN (Virtual Local Area Network) protocol, which is used to separate networks into individual segments, and the switchport mode, which enables switches to assign VLAN tagging to frames.
Best Practices for Configuring Trunks
When configuring trunks, it is essential to follow best practices to ensure optimal performance. Firstly, it is advisable to disable all unused ports to prevent unauthorized access. Secondly, it is crucial to ensure that all devices connected to the trunk are running the same trunking protocol to avoid compatibility issues. Lastly, it is necessary to configure the trunk to handle the expected amount of data traffic.
Troubleshooting Common Trunk Configuration Issues
Despite careful planning and configuration, issues can arise when setting up trunks, leading to data transmission errors and network downtime. One common issue is misconfigured VLAN tags, leading to traffic being sent to the wrong VLAN. Other issues that may arise include duplicate IP addresses and incorrect switch settings. Troubleshooting requires a careful investigation of the configuration settings to identify the issue and take corrective action.
Importance of Regular Maintenance for Trunks
Regular maintenance is crucial for the optimal performance of trunks. It is recommended to perform regular checks on the trunk configuration settings to ensure that they are up-to-date and in line with the network requirements. Additionally, it is essential to monitor the traffic flow through the trunk to identify any potential issues and take corrective action before they escalate. Regular maintenance also involves updating the trunking protocols to the latest versions to take advantage of new features and performance improvements. Failure to perform regular maintenance can lead to network downtime, data loss, and security breaches.
Types of Trunks and Their Uses
There are different types of trunks, each tailored to meet specific communication needs. One type of the trunk is the analog trunk, which is ideal for voice communication systems, while the digital trunk is suited for more complex communications, such as video and data transmission. Another popular type of trunk is the Session Initiation Protocol (SIP) trunk that enables companies to connect their local phone system to the public telephone network over an IP network, reducing call costs.
Analog vs. Digital Trunks: Which One is Right for Your Business?
Analog and digital trunks have unique advantages and disadvantages depending on the specific needs of a business. Analog trunks are typically less expensive and ideal for small businesses that require basic voice communication. Digital trunks, on the other hand, are more expensive but offer a host of features that make them ideal for businesses that need to communicate on a larger scale with multiple types of data. Digital trunks can support telephone, video, and data transmissions, making them a more versatile option than analog trunks.
SIP Trunking: The Future of Business Communication
SIP trunking is a popular trunking technology that has transformed business communication by eliminating the need for traditional landlines. SIP trunks use the internet to connect to the public switched telephone network (PSTN) and offer advanced features such as instant messaging, videoconferencing, and caller ID, among others. The benefits of SIP trunking include reduced communication costs, streamlined communication, and increased flexibility, making them a viable option for businesses of all sizes and niches.
Benefits of Analog Trunks
While digital trunks offer more advanced features, analog trunks have their own set of benefits. For one, they are typically less expensive to install and maintain, making them a more cost-effective option for small businesses. Additionally, analog trunks are known for their reliability and simplicity, making them a great choice for businesses that prioritize stability over advanced features.
Hybrid Trunks: The Best of Both Worlds
For businesses that want the benefits of both analog and digital trunks, hybrid trunks offer a solution. Hybrid trunks combine the reliability and simplicity of analog trunks with the advanced features of digital trunks, making them a versatile option for businesses of all sizes. Hybrid trunks can support voice, video, and data transmissions, making them a great choice for businesses that need to communicate in multiple ways.
Maximizing Trunk Efficiency
While trunks are essential in modern telecommunications, their performance is highly dependent on the extent to which they are optimized. There are several ways to maximize trunk efficiency, ranging from load balancing to optimizing trunk utilization.
How to Optimize Trunk Utilization
Optimizing trunk utilization involves managing the amount of traffic that flows through each trunk. This is done to prevent trunks from becoming congested and potentially leading to network downtime or data loss. By carefully monitoring traffic flow, businesses can identify when specific trunks become overloaded and take corrective action by redistributing the traffic load.
The Benefits of Load Balancing Trunks
Load balancing trunks is a way to maximize efficiency by distributing traffic across all available trunks, preventing any one trunk from becoming overburdened. This not only helps to prevent network downtime but also improves overall data transfer rates and reduces the chances of data loss. Load balancing is typically done through specialized software or hardware solutions, and its implementation can vary depending on the specific business requirements.
Securing Your Trunks
Trunk security is a critical consideration in modern telecommunications, particularly for businesses that handle sensitive data. Securing trunks involves following best practices that minimize the risk of unauthorized access and data breaches.
Best Practices for Trunk Security
When securing trunks, it is essential to employ best practices such as using strong authentication and encryption protocols, keeping up to date with software patching, and carefully monitoring network traffic. Additionally, businesses should follow regulatory guidelines set up by relevant governing bodies to ensure compliance and avoid any fines or legal liabilities.
Protecting Against Trunk Fraud
Trunk fraud is a type of telecom fraud where criminals use trunks to make long-distance calls without authorization, leading to unexpected bills for businesses. Protecting against trunk fraud involves limiting access to trunks by unauthorized users, carefully monitoring network traffic, and implementing appropriate authentication and encryption protocols. Additionally, businesses can employ specialized software solutions that can alert them to any unusual call activity and prevent unauthorized access to the network.
Trunking in the Cloud
Cloud-based trunking is a popular option for businesses that prefer flexibility and ease of deployment. Cloud trunks are hosted remotely, removing the need for businesses to manage any on-site infrastructure.
The Advantages of Cloud-Based Trunking
Cloud-based trunking offers several advantages, including lower costs, faster deployment, and seamless scalability. By leveraging cloud-based trunking, businesses can avoid the expense and time investment of on-site infrastructure, allowing them to focus more on their core business activities.
How to Migrate to Cloud Trunking Smoothly
Migrating to cloud-based trunking requires careful planning and execution to prevent data loss and network downtime. The migration process typically involves the selection of a cloud service provider, careful mapping of the existing on-site infrastructure, and the use of specialized software tools to automate the migration process.
Conclusion
Trunking is a critical component of modern telecommunications, and businesses of all sizes can benefit from its efficient data transfer capabilities. By following best practices for configuring, securing, and optimizing trunks, businesses can improve their network performance, reduce expenses, and improve customer satisfaction. Moreover, by embracing new technologies such as cloud-based trunking, businesses can gain a competitive advantage by being more agile, cost-effective, and flexible.